There is an old story about the bank robber “Slick” Willie Sutton. He was asked why he robbed banks. His straightforward response: “It’s where the money is”. The cybersecurity firm Sophos, recently reported that the ransomware ransoms have been increasing rapidly. Per their numbers, Enterprise ransoms have been averaging approximately $2M per attack. Cybercriminals are focusing more on higher value targets than ever before. MSPs are high value targets. MSP RMMs have access to ALL of their customers. Ultimately, it’s where the valuable data is. When those customers are utilizing an RMM with tightly integrated backups, there is a single access point to dozens, hundreds, or even thousands of organizations. Since the RMM is based on agents that are pushed out, the ransomware can potentially push out its malicious code to each of the MSP clients while neutering their backups. This makes MSPs a very lucrative target. It amplifies their efforts while increasing their returns.
The way RMM administrative privileges are compromised are tried, true, and very effective. They take advantage of the way people are wired and their emotions. It starts with targeted spear phishing. The cybercriminals identify the correct person, to whom they report, the types of automated systems they use, etc. They do this by posing as a potential customer. Then they start phishing. It could be an urgent email or text that appears to come from their direct manager, company executive, or an application they use everyday. The email or text likely contains a link that downloads the ransomware or malware, or an attachment that’s infected with it. The email may emulate an alert email from the same RMM program or another that occurs all the time. The targeted person in both cases will likely not check to see if the email or text is what it is supposed to be and clicks on the link or attachment. When nothing happens, they go about their daily tasks and don’t think any more about it. Of course, they’ve just been compromised.
Websites are another avenue of stealing administrative privileges. These malicious websites sole purpose is to draw the target in to click on a malicious link. The cybercriminals may hijack a legitimate website to accomplish this. Malicious advertising is another pernicious avenue in targeted phishing as is social media and mobile apps. Mobile apps that are actually a front for malicious software that transfer the malware the next time the mobile device connects to a personal computer.
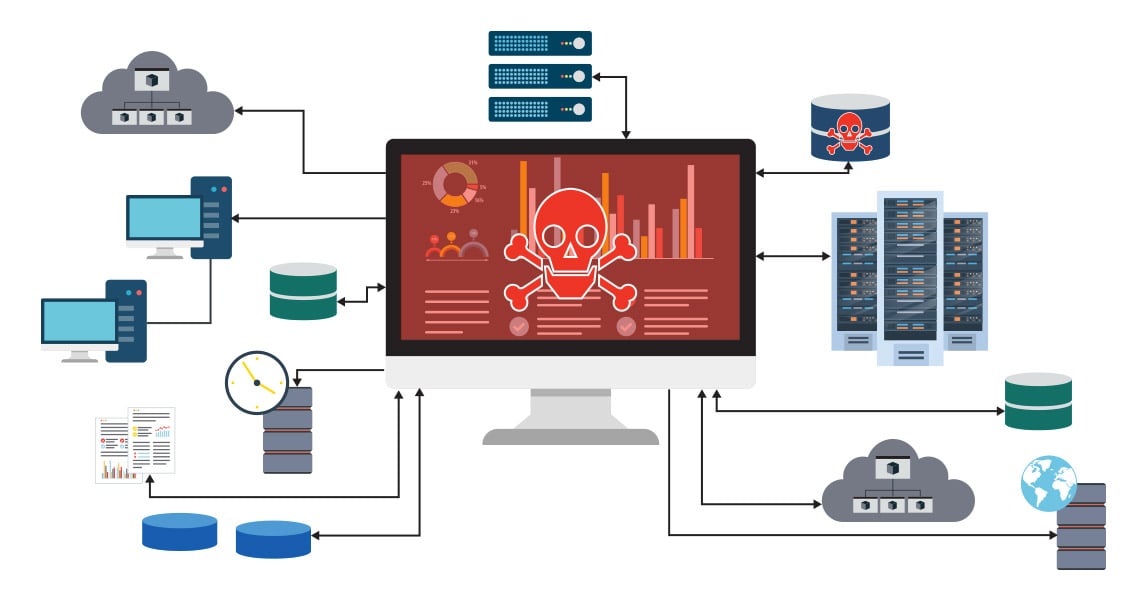
Make no mistake, once the RMM is compromised, so is the integrated backup. Now the entire MSP client base is under dire threat. A threat so powerful it has the potential to cause the MSP to go out of business. In 2019, an MSP was attacked via RMM concurrently encrypting 1,500 to 2,000 systems, facing a $2.6 million USD ransom. Not many MSPs can survive that level of unexpected cost. The MSP remains anonymous and there is no information whether or not they are still in business. Here is an example: MSP RMM Ransomware attack. As a side note, cyberinsurance is exceedingly unlikely to pay that amount of ransom. Late December 2019, the large MSP Synoptek suffered a similar massive ransomware attack. Simply put, MSPs have become a very financially rewarding target. And RMM has become a popular attack vector.
How to Mitigate the RMM Risk
First and foremost, train all employees to be aware of targeted phishing attacks. Regrettably, there is no patch for human carelessness or stupidity.
Next, do NOT have the data protection or backup software tightly integrated with the RMM. Make the cybercriminals work harder to compromise the MSP organization and its clients.
Third, utilize backup software that prevents ransomware or any malware from ever deleting the backups. More importantly, make sure the software prevents a ransomware or malware infection, especially before detonation, cannot be backed up or recovered…period.
Taking these 3 steps will mitigate the RMM risk. Asigra software prevents backups from being deleted via multiple layers of protection including: retention immutability, multi-factor authentication, passwordless biometric authentication, ability to rename the backup directories, and a soft-delete that doesn’t remove the backups for an administrator set timeframe. It is also the first and only data protection/backup software today that prevents malware and ransomware from being backed up or recovered, successfully stopping attack-loops.
To Learn More
Contact us at info@asigra.com