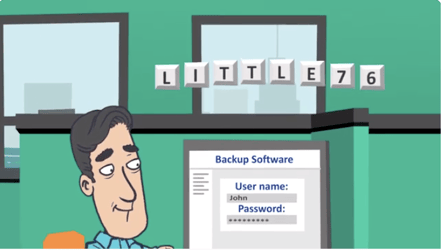
You’re Locked Out Of Your System. What’s Your Next Step?
Today, law practices rely on a growing constellation of devices, networks, locations, physical and virtual machines, and SaaS solutions with a range of data storage protocols. You may not be able to stop malicious code from entering your environment, but you can hunt it and eliminate it — even advanced ransomware hiding dormant in your backups. With Asigra’s Tigris Secure Backup Platform, real-time malware prevention isolates malicious code and alerts administrators of infections.