Your Backups Are Under Attack.
Confidently Defend Them.
Our Customers Include






The Problem Today
Cybercriminals are becoming increasingly sophisticated with their attacks. They know that the only thing standing between them and your willingness to pay is your ability to recover data in the event of a successful ransomware attack.
That's why they now target your backups. If you use a solution that relies on Immutability or Air-gapping alone to protect your backups, you're still vulnerable to attacks.

A Proactive Approach to Backup & Data Security
-
The New Dormant Attacks
Advanced ransomware attacks utilize trojan horse strategies with detonation delays of weeks or months, ensuring that the dormant malware is implanted in all backups (even air-gapped and immutable).
-
Attack Loop
When dormant ransomware finally detonates and a data restore begins, the ransomware hidden in the backup is restored along with corporate data and you are caught in an attack-loop.
-
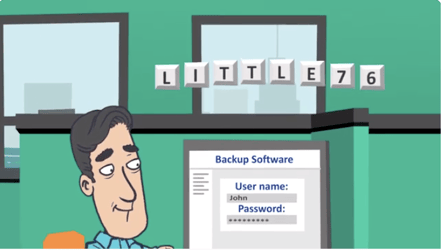
Credential Hunting
Advanced phishing attacks now hunt credentials to gain network access. Attackers can then use the backup system against itself to delete backups and lock out legitimate users.
Asigra Stands at the Intersection of Backup & Security
Asigra takes an entirely different approach to protecting your backup data — a multilayered, proactive approach featuring industry-leading ransomware scanning and other advanced security safeguards. Asigra is designed to hunt and terminate attacks that target your backup data.
increase in financial losses from ransomware between 2020 and 2021 - FBI
increase in the number of ransomware victims between 2020 and 2021 - FBI
average time between a cyber breach and detection - IBM & Ponemon Institute
Asigra Backs Up All of Your Application Portfolio