Detect Deeply Embedded Threats in Multilayered Files with CDR Scanning
Cybercriminals are continuously adapting their methods to infect your systems with ransomware. The new breed of attacks includes deeply embedded executable objects hidden in everyday documents like PDFs, Office macros, and media files that even advanced antimalware scanning can miss.
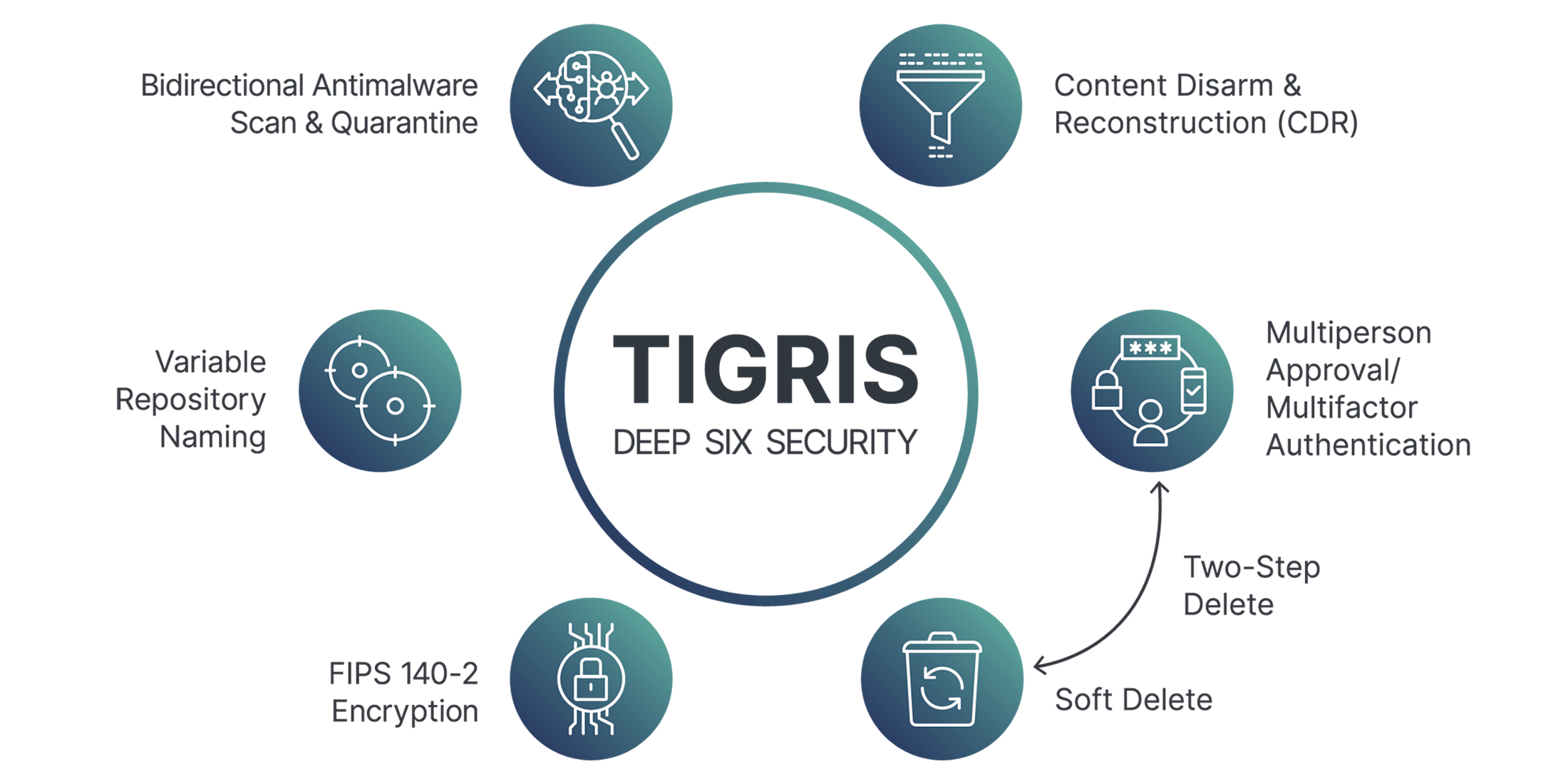
Content Disarm and Reconstruction (CDR) is an innovative feature that deconstructs documents and strips them of any potentially malicious code. Then, the file is reconstructed back into a functional file without the embedded threat
CDR is relatively new to security practices and typically deployed at the gateway to catch incoming files, but it only takes one file getting past your “secure” front door to start an attack.
Asigra Tigris is leading in secure backups by including CDR as part of the backup and restore process to ensure that backed up or recovered files are safe.
You can scan your backups for potentially malicious or unauthorized content based on predefined policies. Active content is reported on during the backup process and filtered, blocked, or removed during the restore process based on your desired policy.